Insights and Trends:
A Technology Blog by RCG
When Good Enough IT Starts Holding Businesses Back
Most IT environments don’t fail overnight. Instead, small inefficiencies, outdated processes, and workarounds build up over time. Learn how “good enough” IT can quietly create friction, slow growth, and hold your business back.
IT Environment Review: What Most Miss
Everything may look “fine” on the surface, but that doesn’t mean your IT environment is working as it should. Many organizations operate with hidden inefficiencies, outdated design, and silent risk that builds over time. Here’s why stable doesn’t always mean healthy.
IT Infrastructure Assessment: Why Nothing Seems Broken (But Still Feels Off)
Everything may look “fine” on the surface, but that doesn’t mean your IT environment is working as it should. Many organizations operate with hidden inefficiencies, outdated design, and silent risk that builds over time. Here’s why stable doesn’t always mean healthy.
Why “It’s Working” Isn’t a Strategy for IT Infrastructure
Many IT environments look stable on the surface. But hidden infrastructure gaps often go unnoticed until pressure exposes them. An IT infrastructure review reveals what lies beneath.
Security Under Pressure: Lessons Every Industry Learns
Security problems aren’t created under pressure — they’re revealed. Learn what audits, outages, and renewals expose about cybersecurity readiness
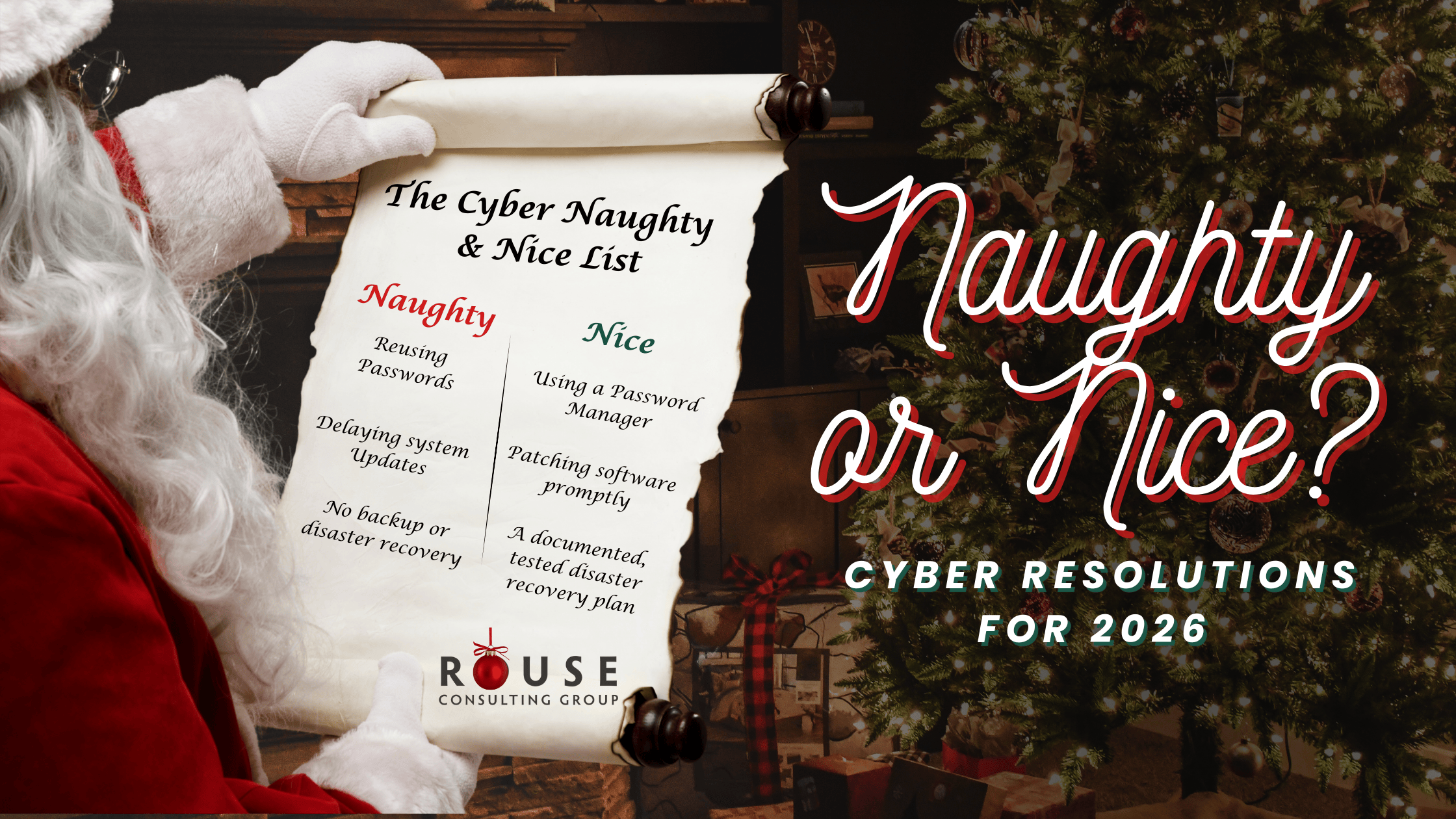
Secure by Design: Start the Year Protected
As the year comes to a close, now is the time to review everyday cybersecurity habits. Explore the full Cyber Naughty & Nice List for 2026 and use this checklist to identify risks and start the new year more secure.
Cyber Naughty & Nice List for 2026
As the year comes to a close, now is the time to review everyday cybersecurity habits. Explore the full Cyber Naughty & Nice List for 2026 and use this checklist to identify risks and start the new year more secure.
Cyber Resolutions for 2026: Naughty or Nice?
Fall is the perfect time to reset your IT strategy. From patching systems and refreshing employee training to testing backups and planning budgets, here are five priorities that can strengthen your security and prepare your business for what’s ahead.
Simplifying Complexity in Healthcare IT
Fall is the perfect time to reset your IT strategy. From patching systems and refreshing employee training to testing backups and planning budgets, here are five priorities that can strengthen your security and prepare your business for what’s ahead.
4 Habits to Strengthen Your Cybersecurity
Fall is the perfect time to reset your IT strategy. From patching systems and refreshing employee training to testing backups and planning budgets, here are five priorities that can strengthen your security and prepare your business for what’s ahead.